
Cyber Strategy: Defense in Depth
Defense in Depth, conceptually, is described in such a way that layered security increases the security of a system as a whole. In the event where one system is compromised, other mechanisms provide the necessary security to protect the system.
It is the antithesis of a singular point of failure, and actively avoids this situation from happening.
In my research, I came across a paper called “Defense in Depth: An Impractical Strategy for Cyber World.” In it, the author’s opinions spoke upon the idea that concept of “Defense in Depth” is unsustainable.
When I first read the concept, I harshly disagreed, as Defense in Depth is a proven industry best practice. The author describes Defense in Depth as the following:
“Defense in Depth was developed to defend a kinetic or real world military or strategic assets by creating layers of defense that compel the attacker to expend a large amount of resources, while straining supply lines. The tactical goal is to delay and render the enemy attack unsustainable. This strategy results in leaving the attacker vulnerable for counter attack. The defender is then able to counter attack the enemy and eliminate the threat.”
Defined in the easiest and redundant way possible, Defense in Depth is the practice of delaying the advance of an attacker. It’s built upon having layers of defensive lines, and relies on the attacker to lose momentum over time as they progress further within. Once an attacker has lost momentum, defensive counter attacks are launched to take out the enemy.
This is commonly referred to as the “castle approach” or sometimes the “onion approach” due to the fact that it relies upon layers of security.
The tactics behind this methodology are sound, and as a human being is the same way that I approach my tactics while playing a game of Risk with friends.
“Defense in Depth, in its original concept, works for a kinetic world defense. The problem with Defense in Depth in the world of Cyber-Defense is that it is unsustainable.”
In a military situation, this approach is highly effective, and it works for one simply fact:
“The defender is then able to counter attack the enemy and eliminate the threat”
It’s at this point where my thought process had changed. Performing a true counter-attack (and not defending against an ongoing attack) would be incredibly hard to swing up the ladder. On top of the various lines of red tape that are in the way, there simply aren’t the available resources that could be used to perform a counter attack. Various costs would come into play, and public image in the event that a counter attack would fail could be catastrophic.
So, one would have to ask themselves…are we really practicing the true form of Defense in Depth? We cannot effectively complete the mission, as we cannot take the threat out of the equation.
At the time of writing this blog, it’s 2016. This paper first hit the web in 2012. According to the Verizon 2015 Data Breach Investigations Report, there were a little over 2,122 confirmed data breaches, from data compiled and reported from 70 contributing organizations, spanning 19 different industries. This was all just from 2015.
It’s difficult to really put into perspective, because on one hand, boy that’s a lot of numbers, but on the other hand, there are many variables that come into play. The biggest contributing factor is that technology is advancing at a furious rate. At the same time, at least in the public sector, technology isn’t advancing at the same rate. Companies don’t upgrade their systems right away, and legacy software/hardware is fully functional and unprotected.

Servers, code bases, all alive with documented and exploitable issues, just waiting for the right hacker to discover.
“The value associated with the attacker’s successes is increasing.
The frequency of successful attacks is increasing.
The effort required to succeed is decreasing.
The skill level required to succeed in an attack is decreasing.”
IT Security Professionals are fighting a battle of limited People, Process, and Technology against an “infinite supply of attackers, with near infinite resources.”
The best we can do as IT Security Professionals is adapt given what resources we have available. An alternative theory, Defense in Breadth, poses the idea that what is missed with one product, can be caught by another. Firewalls, IPS, and Antivirus all factor into this theory.
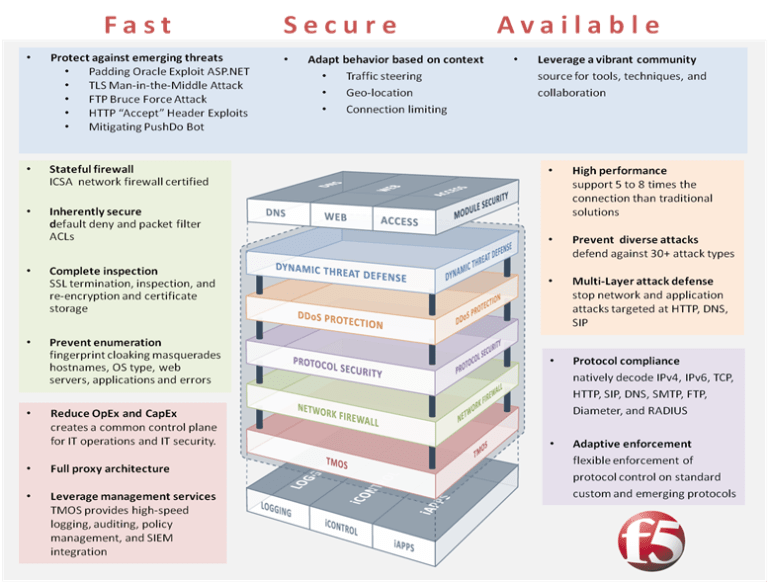
F5 Friday: Goodbye Defense in Depth. Hello Defense in Breadth.
This theory can be applied on the application level. For example, products exist that scan source code as a programming creates their code. By pushing to have a review BEFORE the code review, we can effectively create an environment where secure by design is being followed.
Defense in depth is a concept that should not be ignored, but should be adapted. That is to say, I don’t feel that it shouldn’t be used while implementing your risk strategies. It should be factored into your strategy, while always remembering that you cannot, and won’t destroy the attacker. There will always be a new attacker, and there will always be a way around what you have setup. The best way we might be able to handle future attacks is to adapt the strategy to include defense in breadth tactics, while applying the same endgame defense in depth tactics at the late stage.
In order for this to occur, the professionals need to be able to give their expert opinion to hit multiple levels within a function. One idea that the author posed is for not-for-profit groups like ISSA or Infragard (both groups I recommend every IT Security Professional to become a part of) to act as brokers of data that companies can use for research to generate solutions and improve their own security.
“The primary solution is for Information Technology Security Professionals to start talking and questioning the Status Quo and driving change”
Which can be difficult, but not impossible in your market. I believe that within the next few years, we will see big change within various industries towards a shift to adapt to emerging threats. As big data breaches seem to be on the media at an accelerated pace, Security Leaders will need to make the changes in order to secure their environments.
As a takeaway from all of this, we must remember that we are all on the same team, working towards the same goal. By helping push a change in the status quo, and adapt to the new threats on the market, we can protect our team by driving innovative solutions to preexisting practices.
I’d like to say that I’m not proposing this as a solution, but as a means for discussion, and I hope that this generates some thought on the current environment that security professionals are facing.

Twitter: @ColinSchloth
Guest author Colin Schloth is a Security Engineer currently working in the financial industry with expertise in web application vulnerability assessment, penetration testing, and vulnerability management and remediation. Outside of his professional experience, he focuses on expending his knowledge on Vulnerability Research and Analysis, as well as other areas of the field, such as Cyber Security Offensive and Defensive Strategy.
