Multi-Factor Authentication – Utilizing Keystroke Dynamics
For those of you who are new to the topic, multi-factor authentication is a security system that requires more than one method of authentication from different categories in order to verify the identity of a user. MFA is becoming increasingly popular (if not necessary), especially when looking at the data presented in the Verizon Data Breach Investigation Report. As we saw before, 51% of web application attacks involved the use of stolen credentials. Regina Dugan, vice president of Google’s Advanced Technology and Projects group, said it very eloquently, “Authentication sucks. Passwords suck”.
I’m sure you’ve come across MFA in one form or another. A common example is a website requiring a one-time password after entering your username and password, sent by the authentication server to your phone or email. Authentication factors can be broken down into 3 categories:
- Something you know (password, pin number, secret questions)
- Something you have (one-time password, security token, ID card)
- Something you are (retina scan, fingerprints, voice recognition)
Another category is emerging related to where you are. For example, if you login to a website from New York at noon, it’s impossible for you to login again from London at 2 P.M. If you’re a security professional, I’d highly suggest finding some further readings related to the topic and possibly implementing MFA requirements for applications containing highly sensitive information. MFA significantly decreases the threat of a user’s credentials being stolen because it becomes incredibly difficult (if not impossible) to replicate the additional authentication factor.
I think one form of multi-factor authentication that is particularly interesting is utilizing keystroke dynamics as the second authentication factor. Keystroke dynamics can be described as the pattern or rhythm that a user types on a keyboard. This can also incorporate which non-character keys are used (for example, when capitalizing a letter do you use the right-shift, left-shift, or caps lock). Think about how you type your password, do you see a certain pattern as you type?
I did a lot of research into this for my senior thesis and it’s a very interesting and powerful method of authenticating a user. Technically, this would fall under the category of bio-metrics because it is a characteristic of the user. The process of determining the identity is relatively easy using this method. Let’s use Bob as an example:
- The mystery user types at 60 words-per-minute while Bob types at 40 words-per-minute. The mystery user cannot be Bob.
- The mystery user enters the numbers using the number pad while Bob enters them from the top row of keys, the mystery user cannot be Bob.
- The mystery user uses caps lock to capitalize letters while Bob only uses the shift keys, the mystery user cannot be Bob.
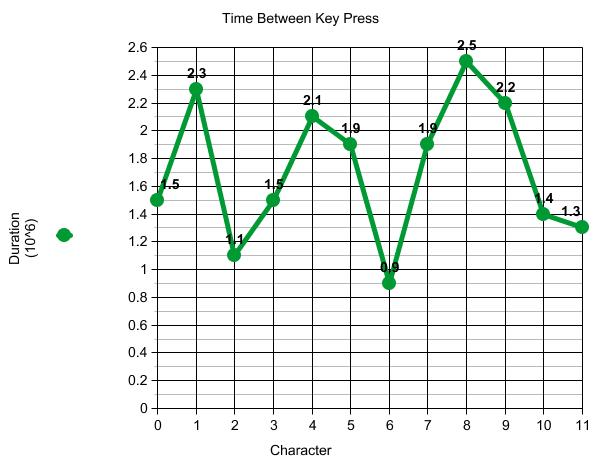
But here’s the best part. These algorithms can be fine tuned on many levels. Even as far as calculating the time between each key press. Of course, this method would require getting averages for each user and calculating in a margin of error, but it provides such a strong level of security. The pattern would look something like this:
What hacker is going to sit there and guess at the infinite patterns that you type your password? Stealing your credentials becomes worthless, and he or she now needs to find a way to bypass the authentication system. Lucky for you, there are some very reputable companies that provide software specifically for this form of authentication. Watchful Software offers a solution called TypeWATCH and Deepnet Security offers TypeSense. TypeWATCH offers continuous protection throughout a user’s entire session while TypeSense authenticates as the user types his or her password.
Of course, all solutions have the benefits and downfalls. In my opinion, the most beneficial aspect is that it doesn’t require an extra step at login. I don’t know if you’ve ever had to tell a development team that they are now required to implement MFA, but the reaction is priceless. It usually goes a little something like this:
Me: So we’ve completed the assessment, and due to the risk surrounding all of the sensitive data in the application we’re requiring an approved form of multi-factor authentication.
Dev: …what’s that?
Me: **Explains MFA**
Dev: Um, that sound expensive and detrimental to the user experience. We’ll have to talk to business about it.
Dev: Yeahhh… business said no.
Me:  I’m sorry, but it’s not an option. We’re merely enforcing policy.
I’m sorry, but it’s not an option. We’re merely enforcing policy.
And insert months of non-stop meetings with executives, every one’s boss, and their mothers. It’s quite the experience. Being able to say that solution does not take away from the user experience makes the process far more bearable. Other benefits and downfalls for keystroke dynamics include:
Benefits
- No additional hardware is required like other forms of bio-metric MFA.
- The user does not rely on another device, like hardware tokens or a business phone for SMS tokens.
- There’s no extra step at login. The user won’t even notice a difference.
- The pattern is extremely difficult (if not impossible) to duplicate. An attacker would have to go to extreme lengths to have a chance at replicating the exact pattern.
Downfalls
- A user’s rhythm can vary day to day for multiple reasons (fatigue, new keyboard, etc.)
- Broken finger/hand? Impossible to login (although an administrator may be able the MFA).
- You may want to check with legal about the software. Keep in mind, it is technically a keylogging software.
If this solution sounds like something that could help you or your organization, many companies offer free demos. Check them out and give it a try for yourself.
Thanks for reading!