
Tango Down: Shodan’s Full Potential
Considering the massive response I got from the last post about Shodan, I figured I should do a follow up. Thank you to all who re-tweeted the link, and a big shout out to John Matherly, founder of Shodan, for the publicity. Bro of the year. If you haven’t read through my last post, I highly recommend taking a quick read through. It will get you up to speed on Shodan’s basics and then we can build off of that on this post.
Before I dive into this, remember: make sure you’re wearing your white hat before walking out into the cyber security world. Shodan is meant to be used as a research tool. Manipulating any unauthorized system is illegal, and federal prison is not a fun place to be.
We already know that Shodan is equivalent to having God himself as your search engine for the Internet of Things, but the awesome people over at Shodan have gone one step further. Introducing: Shodan Exploits.

Shodan Exploits is a search engine that provides vulnerability/exploit data from multiple sources (Exploit DB, Metasploit, and CVE). It functions much like we’ve seen previously, using filters and keywords to return detailed and accurate results on systems, platforms, and much, much more. Previously, we just had the gun… now we have the bullets too.
The filter options for Shodan Exploits are as follows:
| Filter | Command | Example |
| Author | author | author:”kingcope” |
| Bugtraq ID | bid | bid:”48581” |
| Exploit Code | code | code:”</D:propfind>” |
| CVE | cve | cve:”CVE-2011-2064” |
| Exploit Description | description | description:”cisco content” |
| Microsoft Security Bulletin ID | msb | msb:”MS16-010” |
| Open Source Vulnerability DB ID | osvdb | osvdb:”86562” |
| Source | source | source:”CVE” |
| Platform | platform | platform:”linux” |
| Port | port | port:”443” |
| Title | title | title:”Apache Win32” |
| Type | type | type:”remote” |
Again, we have a lot to work with here. Lots of fine tuning can be done, and we can make our searches very board or narrow. Let’s start from the beginning and find a good target by using Shodan’s search engine. This time I’ll be scrubbing out any sensitive data since we’ll be diving into some serious exploits. I started with a broad search (hostname) and took a look at the products that were returned: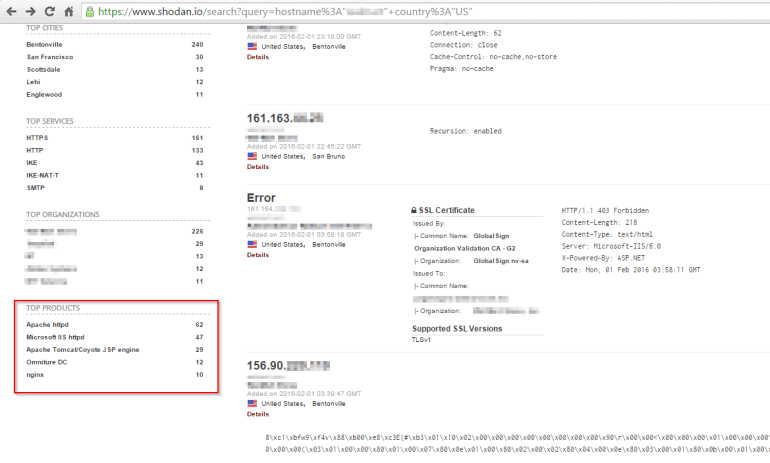
I see some Apache products and Microsoft IIS, but on the right hand side I see Microsoft IIS 6.0. I kind of like the sound of that. Lets drill down into the Microsoft IIS httpd products and see what else is there:

Looks like there’s a few results for version 6.0 as well as plenty of servers running 7.5. I don’t know why the 6.0 interests me so much, but it can’t hurt to dive a little deeper.
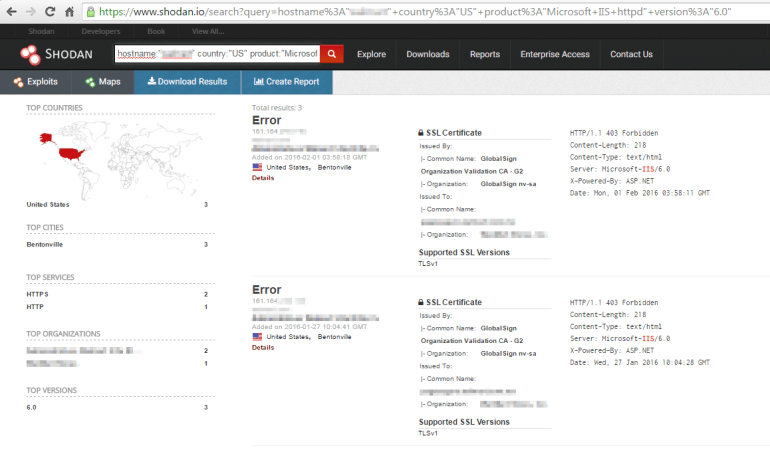
Ahhh yes, those will do. We have two servers running Microsoft IIS 6.0, so let’s head on over to Shodan Exploits and see what we can find there. Let’s just do a broad search for description:”Microsoft iis 6.0″:
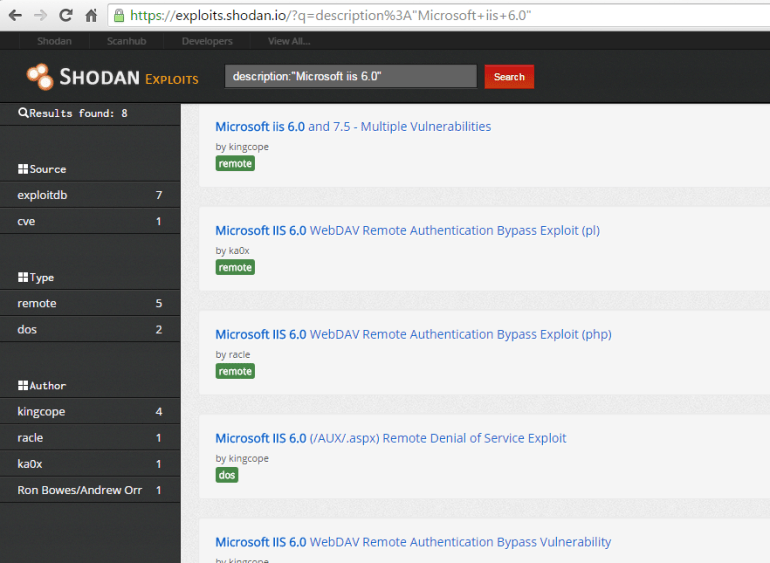
Well then… I’ll just take a look inside the first result:

This is what I find so amazing. We started with a host name and we’ve arrived at a possible exploit. And how long did that take? Shockingly beautiful results. I’m friends with some ethical hackers, and it amazes me when they talk about what they do. Full penetration tests; starting with nothing and finding some way in. This is a tool that makes their jobs 100 times easier, and I’m sure they’re loving it just as much as I am.
I hope you enjoyed reading. Please feel free to share and even leave some feedback, it’s always appreciated.
